This message will probably give you think.
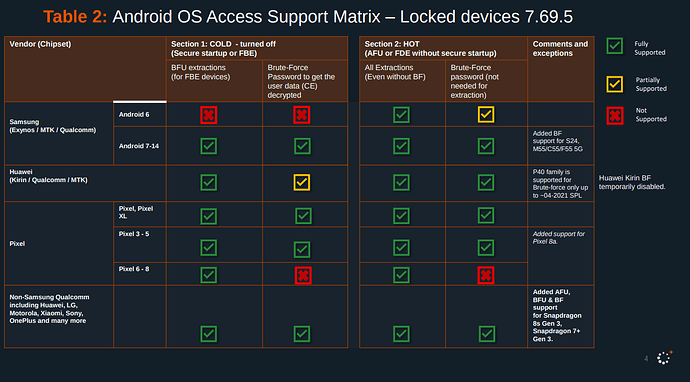
Have you ever considered how easy it is to hack your smartphone? Very easy. Cellebrite can easily access your data in AFU state, and sometimes even in BFU, as in the case of the Serbian activist. Oh, you think Isolated security chip protects your data? This damn chip only stores the keys, but if you trick it into thinking you’ve entered the correct password, it will give them away. Your files are NOT encrypted with your password, which only you know.
Entering the correct password is just a message to the chip to give up ITS own keys, and these are the keys responsible for encryption. If you trick it into giving up the keys, you can get all data.
If phones had double encryption: the first layer is your password, and only the second is the chip key, then a phone in BFU would be completely invulnerable if you have a strong password, since it wouldn’t be stored anywhere, unlike the chip key, and it wouldn’t be accessible. But manufacturers did differently.
You don’t control the encryption. Your password merely signals the chip to release its own keys. The encryption layer is sole. Special agencies will inevitably be able to hack the phone. Even the most secure isolated chip will eventually be compromised by Cellebrite. Sure, you can defending against attacks. But, blocking the USB stack, as GrapheneOS does, is a workaround. The system encryption itself needs to be redesigned, and DirectBootAware mode (introduced by Google), which allows application components to run and variables to be stored outside of encrypted storage, needs to be eliminated. File Based encryption (introduced by Google) also needs to be removed and Full Disk Encryption needs to be restored, as with FileBased Encryption, some system services can be loaded before first unlock. Separating profiles and encrypting them with separate keys is certainly a good idea, but it also expands the attack vector. When system services are running in one profile or on the lock screen, they can be infected, and the next time a password is entered, the data for everyone else can be compromised.
I remember on my old phone, when using Full Disk Encryption and the system encryption feature, the entire system required a password to decrypt after a reboot, and even the lock screen contained nothing but a password entry field. No wallpaper, no time, everything was encrypted. Yes, of course, the old encryption as PROTOCOL was weaker than modern ones, but FullDisk Encryption as encryption TYPE itself was better than File Based Encryption.
For me, the ideal scheme is when encryption is one that uses not only the chip key but also the user’s password, which is stored nowhere except in RAM while the user is using the phone. That’s double encryption. And the RAM keys, whether the chip key or the password, should be erased after each screen off, not just after a reboot. And of course, after each screen off, the entire phone, even system services, remains encrypted (Full Disk Encryption), leaving fewer attack vectors.
You might say that File Based Encryption is supposedly more secure. That’s a lie. No, it’s not more secure. It’s only more secure for separating profiles, not against Cellebrite attacks. Quite the contrary, the threat level has become significantly higher. This is a compromise on security for the sake of convenience. Or perhaps Google is simply collaborating with special agencies. Just like phone manufacturers. For example, how can you explain why they don’t encrypt data using your password? Why your password this is not key, but the key is stored where it can be accessed? The only thing outsiders can’t access is what’s stored in your head.
Even if a password is used to create a key, that may be on modern devices, if that key is ultimately stored somewhere permanently, it is a threat. The password must be a separate layer of encryption and temporarily be stored only in RAM.
In Russian (вариант текста на русском):
Думали ли вы когда-нибудь как легко взломать ваш смартфон? Очень легко. Cellebrite может легко достать ваши данные в состоянии AFU, а иногда даже в BFU, как в случае с сербским активистом. О, вы думаете выделенный чип шифрования спасает ситуацию? Этот гребаный чип только хранит ключи, но если заставить его думать, что вы ввели верный пароль, то он их выдаст. Ваши файлы не шифруются по вашему паролю который знаете только вы.
Верно введённый пароль это лишь послание чипу выдать ЕГО ключи, и именно они отвечают за шифрование. Если заставить его выдать ключи, то можно получить все данные. Если бы на телефонах было бы двойное шифрование: первый слой по вашему паролю, а уже второй по ключу чипа, то тогда телефон в BFU был бы полностью неуязвим если у вас сложный пароль, ведь он нигде бы не хранился в отличие от ключа чипа и его нельзя было бы достать. Но производители сделали иначе. Вы не отвечаете за шифрование. Ваш пароль лишь знак чипу выдать его собственные ключи. Слой шифрования только 1. Спецслужбы обязательно смогут взломать телефон. Даже самый защищённый выделенный чип рано или поздно ложится под Cellebrite. Можно конечно защищаться от атак. Блокировать USB стек, как делают GrapheneOS, но это костыль. Надо переделывать само шифрование системы, а также избавиться от DirectBootAware режима, введённого Google, который позволяет работать компонентам приложений и хранить переменные вне зашифрованного хранилища. Также нужно избавиться от FileBased encryption, введённого Google и вернуться к Fuill Disk Encryption, так как при File Based Encryption некоторые системные службы могут быть загружены до разблокировки экрана, разделение профилей и шифрование их по отдельным ключам это конечно хорошо, но это же расширяет вектор атак, когда в одном из профилей или на экране блокировки работают системные службы, их можно заразить и при следующем вводе пароля просто скомпрометировать данные для всех остальных. Помню на моем старом телефоне при использовании Full Disk Encryption и функции шифрование системы, абсолютно вся система после перезагрузки требовала пароль для расшифровки и даже экран блокировки не содержал ничего кроме поля ввода пароля. Ни абоев, ни времени, все было зашифрованно. Да, конечно старое щифрование как протокол было слабее чем современное, но сам тип Full Disk Encryption был лучше чем File Based Encryption.
По мне идеальная схема это когда шифрование не только по ключу из чипа, но и по паролю пользователя, который нигде не хранится, кроме RAM на то время пока пользователь пользуется телефоном. Тоесть двойное шифрование. А из RAM ключи, будь то ключи из чипа, будь то пароль, должны стираться после каждого выключения экрана, а не только после перезагрузки. Ну и разумеется после каждого выключения экрана абсолютно весь телефон, даже системные службы остаются зашифрованными (Full Disk Encryption), так чтобы оставить меньше векторов для атаки.
Вы можете сказать что File Based Encryption это якобы надёжнее. Это обман. Нет, не надёжнее. Надёжнее только для разделения профилей, но не против атак. Скорее наоборот, уровень угроз стал значительно выше. Это уступка безопасности ради удобства. А возможно Google просто сотрудничает со спецслужбами. Как и производители телефонов. Вот например как объяснить, что они не шифруют данные по вашему паролю? Почему ваш пароль это не ключ, а ключ хранится там где его можно достать? Нельзя достать только то, что хранится в вашей голове.
Даже если для создания ключа используется пароль, что возможно на современных устройствах, если этот ключ в конечном итоге хранится где-то постоянно, это представляет угрозу. Пароль должен представлять собой отдельный уровень шифрования и временно храниться только в оперативной памяти.